Key Takeaways...
- End-of-life IT equipment must be managed as part of a controlled asset disposal strategy to protect data security and reduce security risk. Every device should go through structured lifecycle management so that personal data and sensitive data are removed before any reuse or recycling takes place.
- Certified data destruction is essential for compliance with data protection requirements, especially when handling storage devices that contain confidential business information. Methods such as secure wiping and physical destruction help ensure that no recoverable data remains.
- Effective asset management also improves operational efficiency by tracking equipment from purchase to retirement. This reduces unnecessary costs, prevents outdated systems from remaining in use, and strengthens overall IT governance.
- A sustainable it asset approach supports environmental responsibility by reducing electronic waste and promoting responsible recycling of hardware components. Proper disposal also minimises environmental impact and supports circular economy practices.
- Maintaining chain of custody records and following recognised standards like nist 800-88 ensures that every stage of IT disposal is traceable, secure, and compliant with industry expectations.
- Ultimately, managing end of life IT equipment correctly helps businesses protect data, stay compliant, reduce risk, and build a more secure and sustainable IT environment.
Businesses must protect personal data, reduce security risk, and ensure compliance with data protection standards while supporting sustainable IT asset practices and reducing environmental impact. This guide explains how to handle end-of-life IT equipment in your business with clear, practical steps.
How to Handle End-of-Life IT Equipment in Your Business
Businesses must properly manage personal data, sensitive data, and outdated systems in your business to reduce security risk while improving lifecycle management and operational efficiency.
Managing End-of-Life IT Equipment in Your Business
Managing end-of-life IT equipment in your business requires structured asset management that covers tracking, review, and secure retirement of hardware. Every device must be assessed to ensure it no longer presents a security risk or operational dependency.
Effective asset disposal planning helps organisations control hardware lifecycle stages for end-of-life IT equipment and avoid unnecessary exposure to outdated systems. Many organisations also align internal processes with industry practices to improve structured handling of IT assets across their infrastructure.

Secure Asset Disposal and Data Protection
Secure asset disposal ensures that personal data and sensitive data are fully protected before equipment leaves the organisation. Without proper controls, retired devices may expose confidential information, creating major data protection risks.
When dealing with end-of-life IT equipment in your business, apply strict procedures that include certified data wiping and verification before reuse or recycling. Strong lifecycle management ensures systems are retired at the correct stage, especially when security updates are no longer available, reducing overall data security exposure.
Data Destruction and Physical Security Methods
Data destruction is a critical requirement when handling end-of-life IT equipment. It ensures that all stored information is permanently removed and cannot be recovered.
Certified data destruction methods include secure overwriting and degaussing, while higher-risk equipment may require full physical destruction. Processes such as data destruction are commonly aligned with best practices for eliminating sensitive information from storage devices.
Physical destruction is often used where highly sensitive data is involved, ensuring complete removal of hard drives and preventing any data recovery attempts.
Managing End-of-Life IT Equipment Securely
Managing end-of-life IT equipment effectively reduces operational risk and improves asset control across business systems. Without structured processes, outdated devices may remain in use, increasing vulnerability to cyber threats.
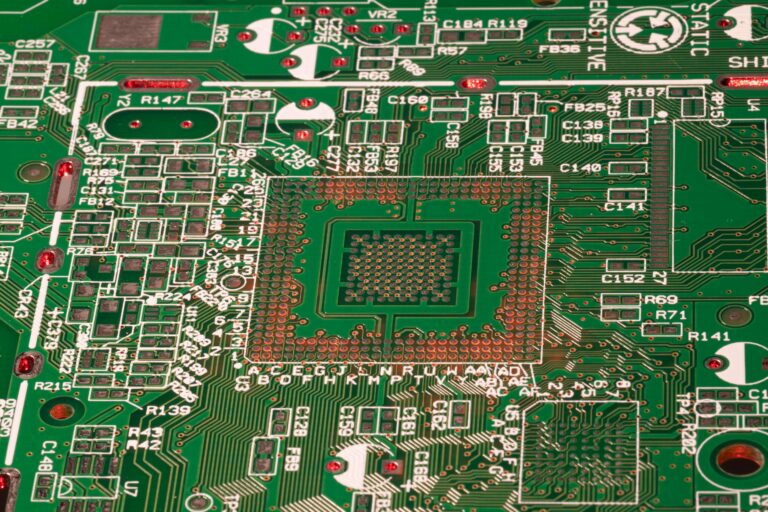
Hardware components such as processors and storage units must be handled carefully during disposal stages. In some cases, recycling methods are used to ensure responsible handling of electronic components while reducing environmental impact.
Chain of custody tracking remains essential throughout the process to maintain accountability and ensure every stage of handling is documented correctly.
Server and Infrastructure Disposal
Enterprise systems require careful handling during disposal due to their complexity and data storage capacity. Servers and motherboards often contain large volumes of sensitive data that must be securely removed before recycling.
Specialised processes are options that support responsible material recovery while maintaining strict data protection standards. This ensures that both hardware components and embedded information are safely managed during end-of-life processing.
Data Security and Risk Reduction
Data security is one of the most important considerations when handling end-of-life IT equipment. Devices in your business often contain personal data and sensitive data that can create a significant security risk if not properly destroyed.
Certified data destruction ensures all information is permanently removed, reducing exposure to breaches and compliance failures. Following recognised standards such as NIST 800-88 ensures consistency in secure data handling practices across all devices.
Environmental Impact and Sustainable IT Asset Practices
Proper IT disposal significantly reduces environmental impact by preventing electronic waste from entering landfills. A sustainable IT asset approach for end-of-life IT equipment ensures materials are reused or recycled responsibly.
Responsible processing reduces demand for raw materials and supports circular economy principles. Organisations that implement structured asset management strategies also improve long-term sustainability performance and corporate responsibility outcomes.
Lifecycle Management and Asset Control
Lifecycle management ensures IT systems are used efficiently from deployment through to disposal. It helps organisations plan upgrades, reduce downtime, and maintain secure infrastructure.
Strong asset management ensures all devices are tracked throughout their operational life, allowing businesses to make informed decisions about replacement cycles. This reduces unnecessary costs while improving system reliability and performance.
Certified Data Processes and Compliance
Certified processes ensure compliance with UK data protection regulations and industry standards. They confirm that all equipment has been securely processed and no recoverable data remains.
In addition to data handling, some organisations also require secure destruction of physical items containing stored information. There are also processes to ensure that devices and components are permanently destroyed where reuse is not appropriate.
A structured approach to end-of-life IT equipment in your business ensures organisations maintain strong data security and operational control. By combining lifecycle management, certified data destruction, and responsible recycling practices, organisations can reduce risk and improve efficiency.
Proper handling of IT assets ensures that sensitive data is protected, environmental impact is reduced, and all systems are disposed of securely and in compliance, supporting long-term business stability.